2. VPN Tunnel Configuration File
Download the VPN configuration file from Amazon and fill it in with your Orka network configuration.
Quick navigation
You are here in the workflow: AWS-Orka Connections | 1. AWS Side of the VPN Tunnel | 2. VPN Tunnel Configuration File | 3. Orka Side of the VPN Tunnel | 4. Verifying the VPN Tunnel | VPN Tunnel Troubleshooting
On this page, jump to: Step 1: Download the file from Amazon | Step 2: Fill in the configuration file
You need:
After you have created your VPN tunnel in Amazon, you need to configure your Cisco firewall to recognize the connection and let traffic into your Orka cluster.
Amazon provides a semi-prefilled configuration file with very detailed instructions. First, you need to download the configuration file and provide the missing information indicated by placeholders. Next, you'll need to feed the configuration into your Cisco ASAv to complete the setup.
Step 1: Download the file from Amazon
- Verify that you are logged in your AWS Management Console and you're working in the correct region.
- Verify that you have created a tunnel in Amazon.
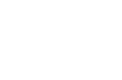
- Navigate to your VPC service. In the VPC service sidebar, locate the Virtual Private Network menu and select Site-to-Site VPN Connections.
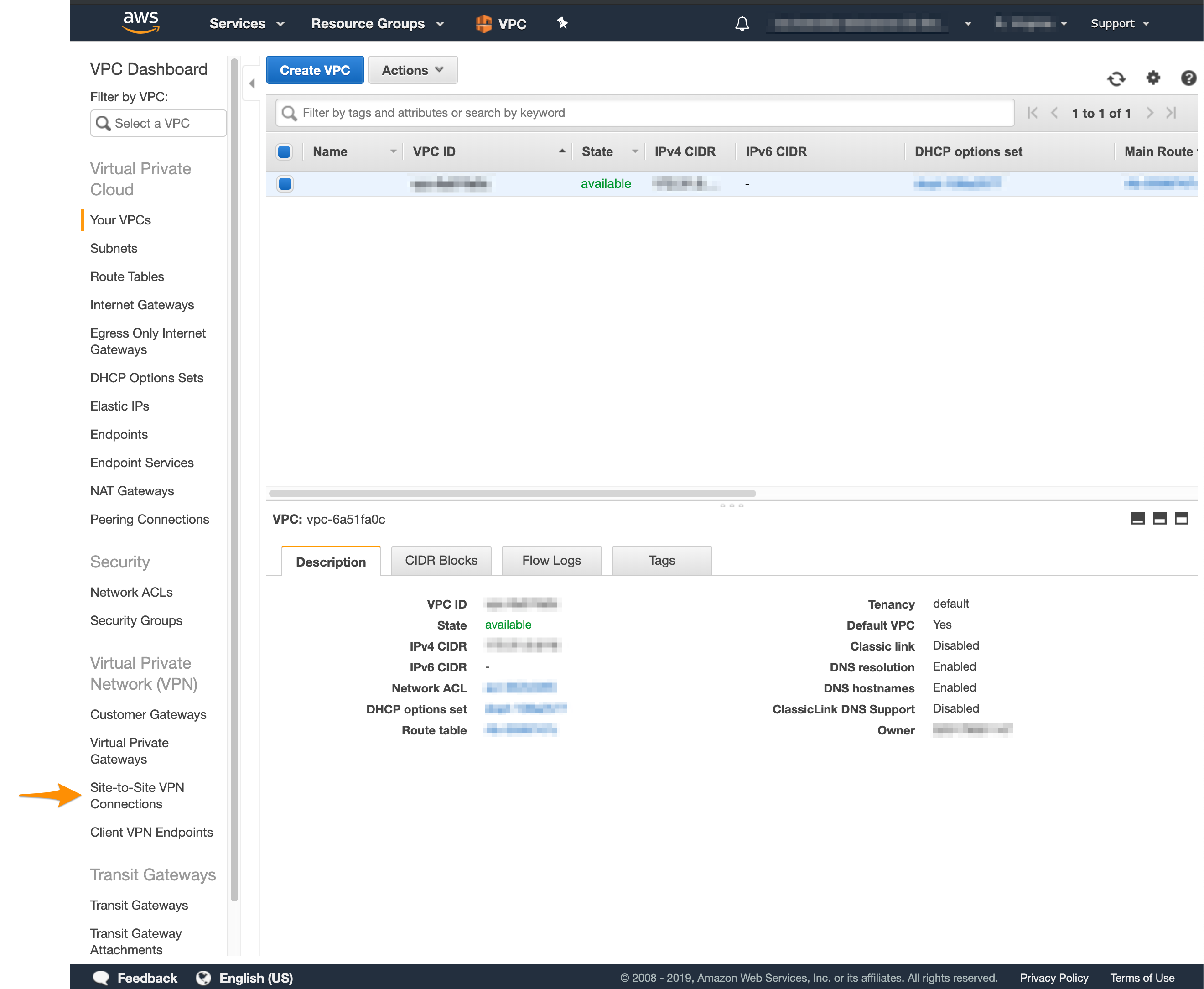
- In the list, select your newly created VPN connection and click Download Configuration.
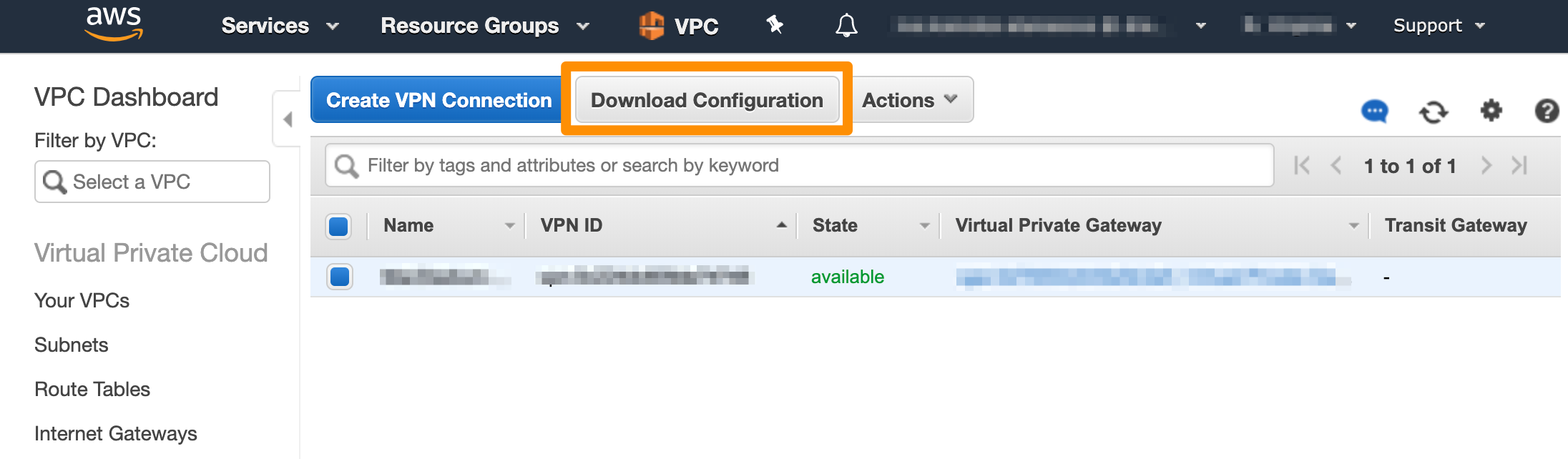
- Fill in the form and click Download.
- For Vendor, select Cisco Systems, Inc..
- For Platform, select ASA 5500 Series.
- For Software, select ASA 9.x for a policy-based VPN OR ASA 9.7 + VTI for a route-based VPN.
Step 2: Fill in the configuration file
CAUTION
Unless you have extensive experience with AWS and ASAv configurations, follow the instructions in the configuration file to the letter. Otherwise, your site-to-site VPN might not work as expected.
- Open the configuration file in a text editor.
- Replace all placeholders with their respective values.
| Placeholder | Value | Description | More information |
|---|---|---|---|
<outside_interface> | Outside | The name of the outside interface of your Cisco ASAv device (the Outside network). | The IP Plan |
<outside_access_in> | (Sample) outside_access_in | Any unique name. This will be the name for the access control list that permits the creation of the tunnel and the traffic over it. | Cisco Documentation: Cisco Access Control Lists |
<vpc_subnet> | (Sample) 192.168.0.0 | The IPv4 address of your Amazon VPC (without the subnet mask bit notation). | You can get this value by selecting your VPC in AWS > VPC dashboard and checking the Details at the bottom of the screen. |
<vpc_subnet_mask> | (Sample) 255.255.0.0 | The subnet mask for your Amazon VPC, converted from its CIDR notation. | You can get this value by selecting your VPC in AWS > VPC dashboard and checking the Description at the bottom of the screen. You need to convert the subnet mask bit notation to the correct subnet mask (e.g., the /16 notation converts to a 255.255.0.0 subnet mask). |
<amzn_vpn_map> | (Sample) amzn_vpn_map | Any unique name for the crypto map. It must not be already in use by any other crypto maps you might have configured. | Cisco Doumentation: Configuring Crypto Maps |
<sla_monitor_address> | (Sample) 192.168.0.1 | An IP address in your Amazon VPC that can serve as an SLA monitor keeping the site-to-site tunnel alive. | You can set this to the <vpc_subnet> address plus one. |
<local_subnet> | 10.221.188.0 | The IP address for the Private-1 network. | The IP Plan |
<local_subnet_mask> | 255.255.255.0 | The subnet mask for the Private-1 network. | The IP Plan |
- Uncomment the following lines. To uncomment, remove
!at the start of the line.access-list amzn-filter extended permit ip ...object- andnat-related configuration at the end of the config file.
- Keep the following line. This ensures the SLA monitor works as expected.
object network obj-SrcNet
subnet 0.0.0.0 0.0.0.0
Note that based on your network configuration and requirements, you can modify this line to map to the subnet and the subnet mask for the Private-1 network from your IP Plan. If you choose to modify this line, do not configure the <sla_monitor_address> value.
- Change
nat (inside,outside)tonat (Private-1,Outside). - (Optional) Delete the remaining commented lines to clean up the file. Commented lines are indicated by
!at the beginning of the line. - Save your changes.
What's next
Updated almost 2 years ago